Zero day exploits are the bane of cybersecurity. These malicious attacks leverage previously unknown vulnerabilities in software, hardware, or systems before patches or mitigations can be deployed. Attackers capitalise on these zero-day weaknesses to gain unauthorized access, steal sensitive data, or disrupt operations with devastating consequences. Because they are unpatched, zero-day exploits pose a significant threat to individuals and organizations alike. Defending against them requires constant vigilance, regular software updates, robust security measures, and a proactive approach to vulnerability management.
This Digital Battlefield
In the dynamic landscape of cybersecurity, the battleground has transcended from physical to electronic. Nations now compete for dominance in the delicate realm of data. Every keystroke can be a strategy, and the stakes are profound. This is where the cyberwarrior conducts their missions, navigating a labyrinth of firewalls. The frontiers are blurred, and the only certainty is that in this arena, the struggle never ceases.
Code Warrior
The path of a Code Samurai is neverending of obstacles. They harness the versatile tools of programming to forge incredible software. Their code are their artifacts, and they fight glitches with grace. The virtual world is their playground, and they remain vigilant against unforeseen issues. A Code Samurai embodies the spirit of a true programmer: driven, with an unyielding desire to solve problems.
Ethical Hacker's Dilemma
An ethical hacker often faces a complex dilemma. While their goal is to expose vulnerabilities and strengthen security systems, the very act of accessing these systems can over step ethical boundaries. They walk a narrow line between protecting data and maybe causing damage. This conflict can lead internal challenges.
Ethical hackers must continuously analyze their actions, guaranteeing they remain inside the bounds of right and wrong. This involves transparency with clients and participants, as well as a strong belief to moral hacking practices.
Blues About the Back Door
Well, ain't that a kick in the pants? You step out for a quick trip down to the corner store/gas station/watering hole, and when you come back, your whole world's been turned upside down/around/sideways. Seems like somebody's been snoopin' around while you were gone, messin' with your stuff. Maybe they stole/borrowed/helped themselves to a few of your treasures/belongings/possessions. Or maybe they just left a big ol' mess for you to clean up/away/out. Whatever the case, you got yourself a good read more old-fashioned backdoor situation, and that ain't no fun at all. You gotta be more careful/watchful/wary next time, friend.
There's nothin' worse than comin' home to find your privacy/peace/quiet violated.
It can leave you feelin' like a sitting duck. You just gotta hope that they didn't take anything too valuable.
{If they did, well, best of luck gettin' it back. You might want to check with your neighbors and see if they saw or heard anything suspicious. Or maybe you could put up a security system/sign/camera as a deterrent for next time.
System Breach
A severe system breach has been detected within the organization's security perimeter. Unauthorized access was gained through a complex attack vector, resulting in the possible compromise of sensitive data. The incident is currently under review by our dedicated security team, who are working tirelessly to address the breach and restore full system stability. We urge all users to remain vigilant and report any suspicious activity immediately.
 Mike Vitar Then & Now!
Mike Vitar Then & Now! Michelle Trachtenberg Then & Now!
Michelle Trachtenberg Then & Now!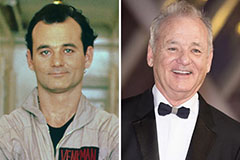 Bill Murray Then & Now!
Bill Murray Then & Now! Dawn Wells Then & Now!
Dawn Wells Then & Now!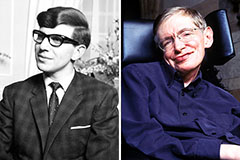 Stephen Hawking Then & Now!
Stephen Hawking Then & Now!